

Keragon is committed to the security of our platform and the protection of our customers' data, including Protected Health Information (PHI). We welcome and encourage security researchers to help us identify vulnerabilities in our systems. This policy describes how to report vulnerabilities to us, what we expect from you, and what you can expect from us.
We value the contributions of the security research community and recognize the importance of a coordinated approach to vulnerability disclosure. If you have discovered a security vulnerability, we encourage you to let us know immediately. We welcome the opportunity to work with you to resolve the issue promptly.
Adhering to industry standards is important to us, and our program is covered by Coordinated Vulnerability Disclosure, Safe Harbor, Open Scope and Core Ineligible Findings, and Detailed Platform Standards
The following assets are in scope:
The following are out of scope:
Keragon considers security research conducted under this policy to be authorized conduct. We will not initiate legal action against researchers who discover and report vulnerabilities in good faith and in accordance with this policy. This safe harbor applies to applicable federal and state laws including the Computer Fraud and Abuse Act (CFAA) and the Digital Millennium Copyright Act (DMCA).
Given that Keragon handles PHI, researchers must observe extra care: never attempt to access, download, copy, or exfiltrate real patient data or PHI. If you inadvertently encounter PHI during testing, stop immediately, do not save or share the data, and report the exposure as part of your vulnerability submission so we can remediate. Keragon will treat any inadvertent PHI exposure discovered through this program as a potential HIPAA incident and follow our Breach Notification procedures.
Keragon's bug bounty program uses a tiered model combining monetary rewards with recognition-based incentives.
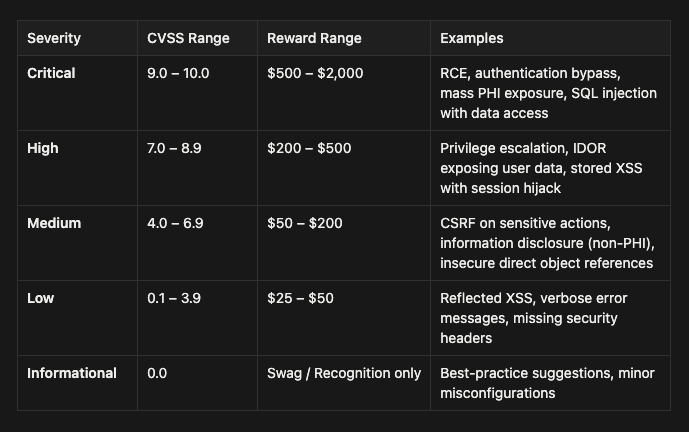
Note: Reward amounts are at Keragon's discretion based on impact, quality of report, and whether a working PoC is provided. PHI-related vulnerabilities automatically receive a severity bonus multiplier of 1.5×.
Payouts: Please note that Keragon is based in the United States, and we are unable to pay financial bounties to residents or those who report vulnerabilities from a country against which the United States has trade restrictions or export sanctions as determined by OFAC. We can still accept vulnerability reports from researchers in sanctioned regions and we can award non-monetary incentives, but no financial payments will be made.
Hall of Fame - A public page listing researchers who have submitted valid reports, ranked by contribution. Includes researcher name/handle, number of valid reports, highest severity found, and date of first contribution.
Swag & Recognition - Branded Keragon swag for first valid submission, personalized thank-you letter from CTO for critical findings, LinkedIn endorsement/recommendation for top contributors.
Early Access - Top researchers get early access to test new features before release.
The following do not qualify for monetary rewards: previously known or duplicate issues, issues already identified by internal scans, vulnerabilities in out-of-scope assets, reports without clear reproduction steps, theoretical vulnerabilities without demonstrated impact.
IMPORTANT - Please note that we are not accepting any new submissions for our bug bounty program at the moment and until further notice. For any critical findings, please use our security at keragon dot com email address.